With Halloween approaching tomorrow, it is an excellent time to take a look at the “Tricks” being played at the doorstep of IT Departments. From more sophisticated cyber attacks to advances in job-killing technologies, 2018 has been a truly scary year for IT Departments.
 Cloud Computing
Cloud Computing
The Cloud has made Enterprise Infrastructure more available for startups, but it also brings with it a plethora of challenges. Cloud computing is fast to deploy and often a more affordable choice for business. However, with Cloud, it relies heavily on the technical capabilities and capacity of the Cloud Services Provider. As we all know, in technology there can be many points of failure that can slow or temporarily disable access. Couple that with today’s modern cyber hacking threats, a strong concern for data privacy, and the appropriate concern in putting so much trust for delivery in another companies hands, Cloud Computing is not an anxiety-free solution for most.
In addition, as local computers are being replaced with lower-resource “cloud clients,” the need for robust traditional IT support teams are in jeopardy. However, the upside is that the demand for people with coding, web and software development, and network security skills and experience are in high demand right now.
 The Human Factor
The Human Factor
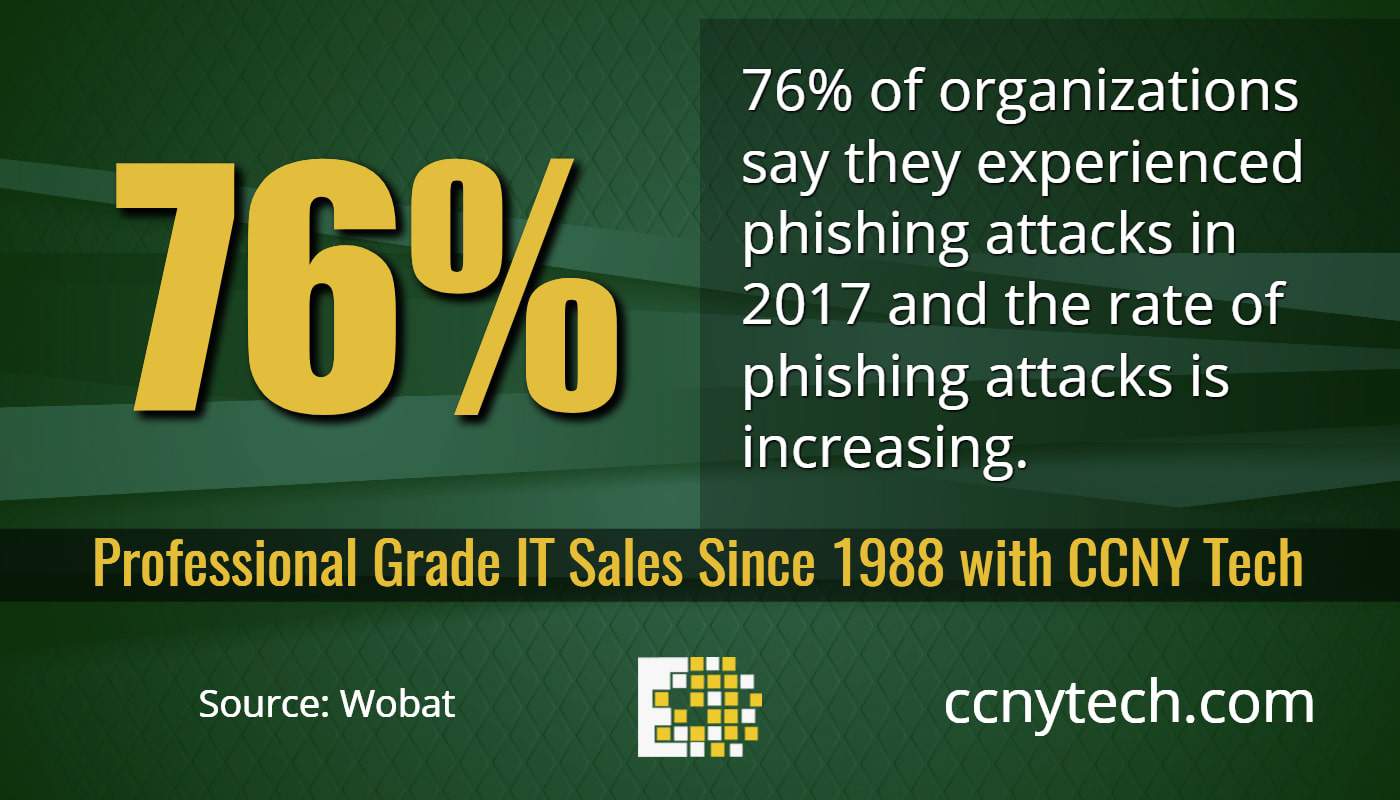
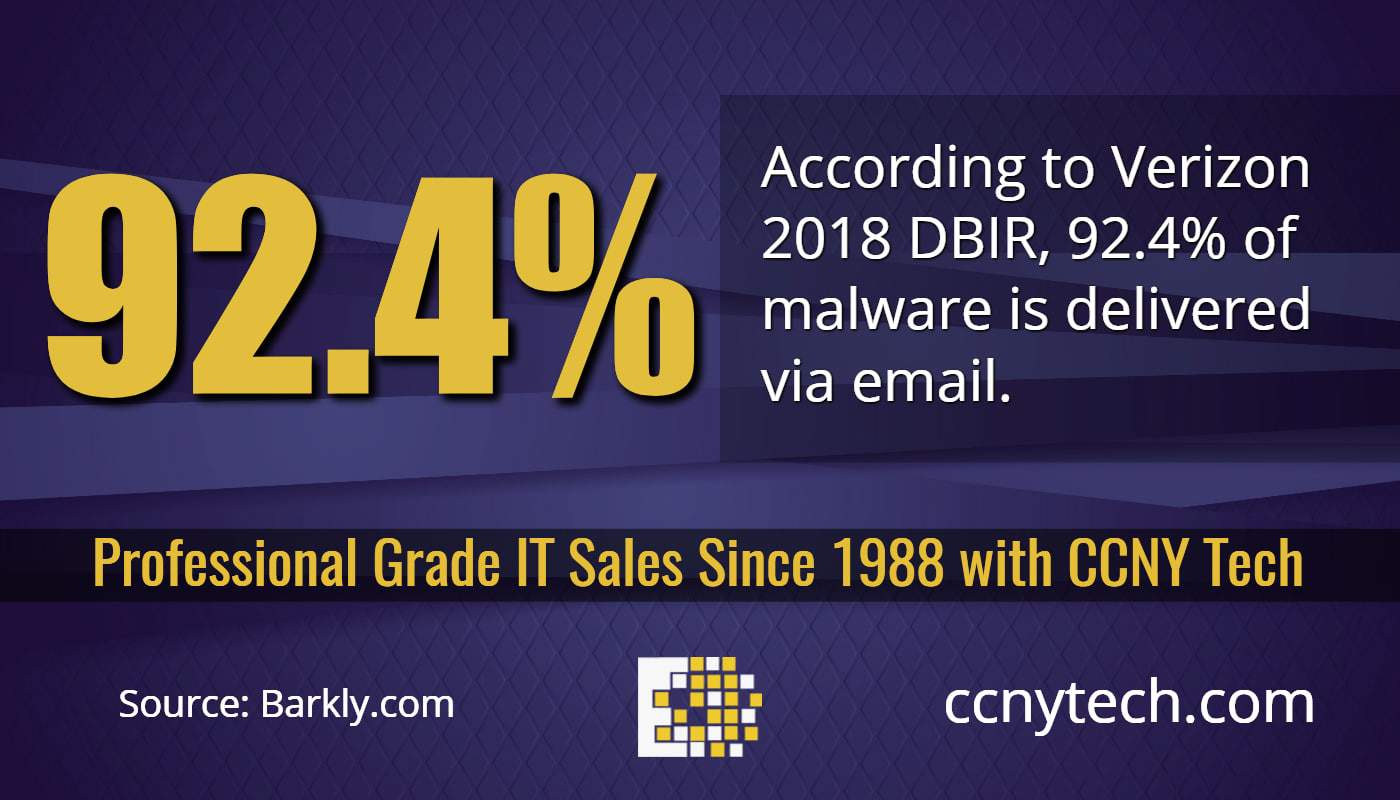
Attempts to trick users into giving personal information spiked more than 500 percent from the first to second quarter of 2018, according to researchers at Proofpoint.
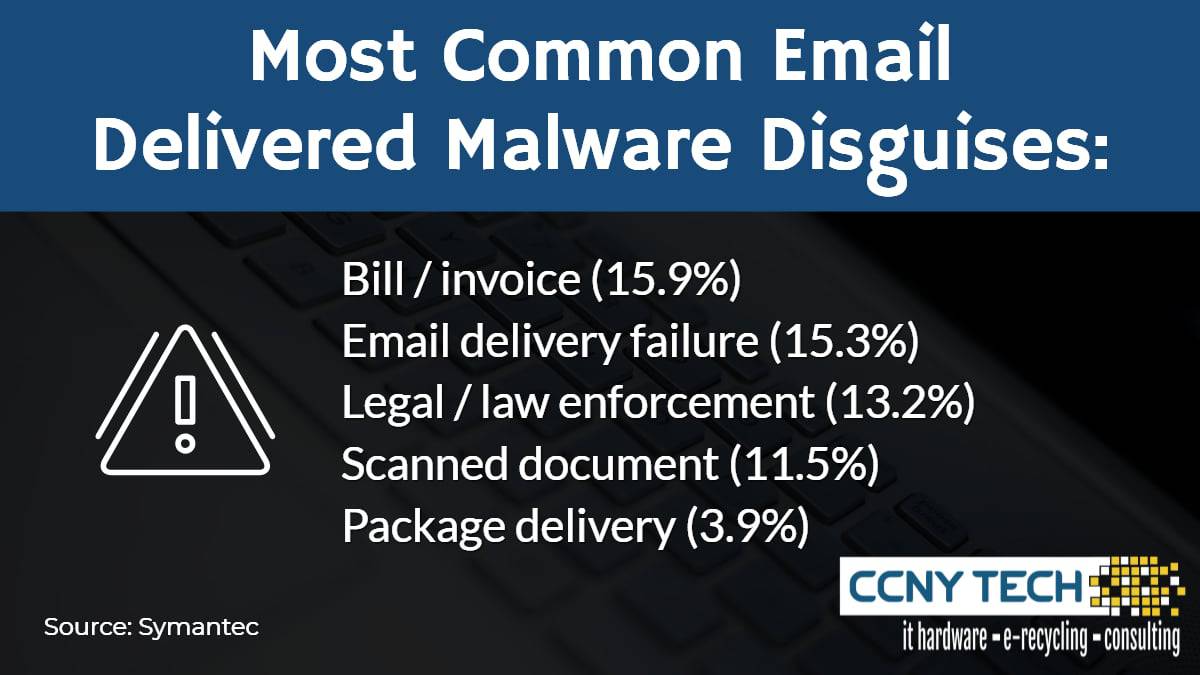
Social engineering is increasingly the most popular way to launch email attacks, and criminals continue to find new ways to exploit the human factor. Typical network security solutions have become more robust and intelligent in recent years, so hackers and mal-intent actors have resorted to the next weakest link… The Human Factor. The responsibility for educating users to understand those threats is a new concern for IT Departments to keep their data and networks secure.
Cryptocurrency & Malware
The use of cryptocurrency, fake antivirus and browser plugins are responsible for the jump in attempts to manipulate users this year. Overall, the volume of email fraud that organizations receive has increased 87 percent year-over-year, and the threat of Ransomware has sky-rocketed this year as cryptocurrency protects the cyber criminal’s identity, while increasing the bounty for them to expand these attacks.
The sad realities in the IT industry may seem scarier each year as companies become increasingly tied to networks and The Cloud for commerce and operations. But on the positive side, self-repairing systems and smaller more efficient processors will open the door for more reliable technology going forward.
 CCNY Tech is a company dedicated to solving IT concerns and delivering the top enterprise hardware and software solutions available. We provide support for the full lifecycle of IT hardware, including the end-of-life disposal. Contact us at 1-800-566-4786 or visit ccnytech.com to learn more about our solutions.
CCNY Tech is a company dedicated to solving IT concerns and delivering the top enterprise hardware and software solutions available. We provide support for the full lifecycle of IT hardware, including the end-of-life disposal. Contact us at 1-800-566-4786 or visit ccnytech.com to learn more about our solutions.
 Cloud Computing
Cloud Computing The Human Factor
The Human Factor CCNY Tech is a company dedicated to solving IT concerns and delivering the top enterprise hardware and software solutions available. We provide support for the full lifecycle of IT hardware, including the end-of-life disposal. Contact us at 1-800-566-4786 or visit
CCNY Tech is a company dedicated to solving IT concerns and delivering the top enterprise hardware and software solutions available. We provide support for the full lifecycle of IT hardware, including the end-of-life disposal. Contact us at 1-800-566-4786 or visit